Free Funnel Audit
Convert more customers today!
SEO
10 mins read


SEO
10 mins read


Ranking on page one is no longer optional in cybersecurity. If prospects cannot find you, they will find your competitor.
You work in a highly competitive cybersecurity market. Buyers expect proof before they trust you. You cannot rely on basic SEO methods. You need focused Cybersecurity SEO built for security buyers.
Many security firms publish content but see weak results. That happens when intent is ignored. Security buyers research carefully and compare vendors. Your content must support that process.
This guide shares eight clear tactics you can apply. Each tactic is practical and structured. You will learn how to attract qualified leads who are actively searching for security solutions.
You will also build long-term authority that earns trust, strengthens brand credibility, and drives consistent inbound growth.
Cybersecurity SEO operates in a very different buying environment. You deal with long sales cycles where buyers rarely decide after one visit. Most prospects review several vendors, compare approaches, and validate claims before moving forward. Your content must support multiple decision stages, from early research to final approval.
Your audience also thinks differently from regular consumers. Many readers are CISOs, IT managers, or compliance leaders. They focus on risk exposure, security gaps, and system impact. They want clarity, technical accuracy, and real proof, not emotional persuasion or vague benefits.
Compliance makes your messaging more sensitive. Buyers care deeply about SOC 2, ISO standards, and regulatory alignment. They examine data handling practices closely. Any sign of overpromising can damage trust quickly and stop the buying process.
Your services are technical and complex. MDR and SOC monitoring need clear explanations that reduce confusion. IAM and penetration testing require real use cases to show outcomes. At the same time, competitors often have strong domain authority. To compete, you must use structured content and build authority steadily over time.
Factor | How Cybersecurity SEO Is Different |
Sales cycle length | Buyers take longer to decide and revisit content multiple times. SEO must support long-term nurturing. |
Audience profile | Readers are security and compliance professionals, not casual consumers. |
Decision focus | Risk reduction, threat exposure, and system impact drive decisions. |
Trust requirements | Accuracy and proof matter more than persuasive language. |
Compliance pressure | Messaging must align with SOC 2, ISO, and data governance standards. |
Claim sensitivity | Overpromising damages credibility faster in security markets. |
Service complexity | Technical offerings need simple explanations and clear structure. |
Use-case importance | Real scenarios help buyers understand value and outcomes. |
Competitive authority | Many competitors already rank well and hold strong backlinks. |
Content strategy | Success depends on structured pages and steady authority building. |
Below are the core cybersecurity SEO tactics that help build trust, authority, and long-term growth. These tactics focus on long sales cycles, technical buyers, and strict compliance needs. Each tactic supports a different stage of the buyer journey and strengthens credibility over time.
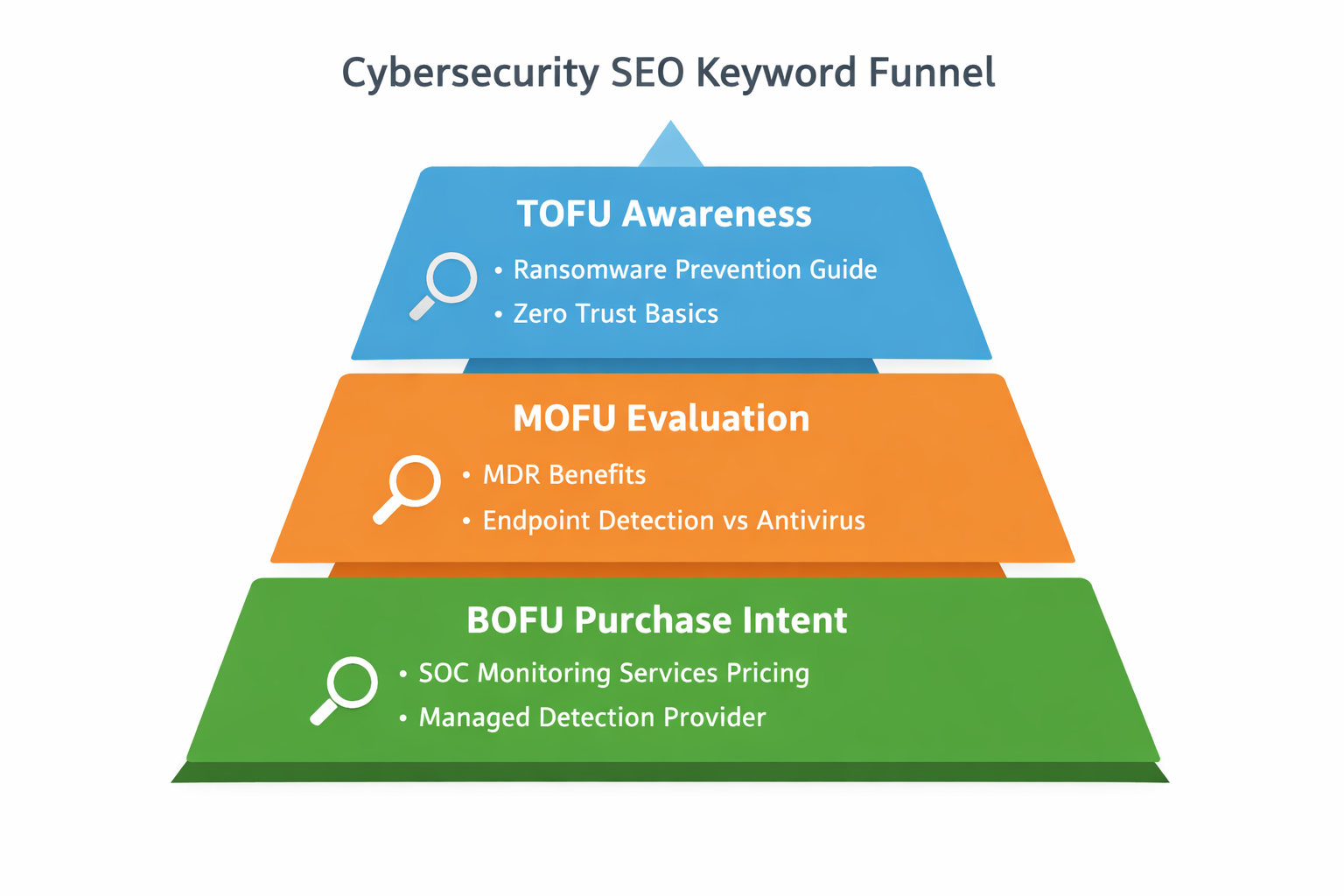
Alt text: Cybersecurity SEO keyword pyramid showing TOFU, MOFU, and BOFU stages.
You need a clear keyword structure before creating content. Random targeting wastes effort and budget. A structured plan supports steady growth.
Group related keywords into focused clusters. Each cluster should center on one service theme. This improves clarity and authority.
In Cybersecurity SEO, keywords must match buyer intent. Divide them into three stages.
TOFU keywords focus on awareness.
Examples include ransomware prevention guide or zero trust basics.
MOFU keywords focus on evaluation.
Examples include MDR benefits or endpoint detection vs antivirus.
BOFU keywords focus on purchase intent.
Examples include SOC monitoring services pricing or managed detection provider.
Identify feature-based keywords that highlight capabilities. Examples include ransomware protection software. Service-based terms describe delivery models, such as penetration testing services.
Include comparison and compliance-driven keywords. These attract serious and risk-focused buyers. Map every keyword to a buyer role. CISOs, founders, and IT managers search differently.
When choosing cyber security SEO keywords, focus on intent first. Relevance matters more than search volume. A clear structure makes growth measurable.
Traffic alone will not grow revenue. You need content built for buying intent. Bottom-of-funnel pages attract serious prospects.
Create focused landing pages for each service. Do not mix unrelated services together. Clear pages convert better.
Build comparison pages that answer direct questions. Buyers search for vendor alternatives and comparisons. These pages support final decisions.
Create “Best X for Y” pages for specific industries. For example, best MDR for fintech companies. These pages attract high-intent traffic.
Develop industry use-case pages such as:
Each page should address real risks and compliance needs. Speak directly to that industry.
Place clear calls to action on every page. Keep them visible and simple. Add strong trust signals such as:
Effective Cybersecurity SEO connects rankings with revenue. Transactional pages help you turn traffic into qualified leads.
Security buyers expect detailed explanations before making decisions. Surface-level content will not build real trust. Authority grows when you explain complex topics clearly.
Publish in-depth guides on advanced subjects. Examples include SOC 2 readiness planning. Another example is Zero Trust implementation steps. You can also compare MDR vs EDR clearly.
These guides should explain systems in simple language. Break down technical ideas into understandable parts. Use diagrams and architecture visuals where helpful. Visual clarity improves comprehension and engagement.
Framework-based explanations also build credibility. For example, outline incident response stages clearly. Explain threat detection workflows step by step. Provide structured insights instead of marketing claims.
E-E-A-T is critical in this niche. Experience and expertise matter greatly. Show real-world understanding of security operations. Cite examples of common threat scenarios.
Include technical contributors when possible. Feature security consultants or engineers as authors. Add short bios highlighting certifications or experience. This builds credibility with technical buyers.
High-ranking security websites often demonstrate deep knowledge. They provide educational value beyond selling services. Authority signals help search engines and readers trust your content. In cybersecurity, trust directly influences buying decisions.
Pro Tip: Work with SEO professionals and technical contributors. Feature security experts with short bios to build trust. In cybersecurity, authority and credibility directly influence buying decisions.
Technical foundations must be strong before scaling content. Security buyers expect fast and secure browsing experiences. Poor performance weakens credibility immediately. A structured checklist keeps your site reliable and efficient.
Use this technical checklist to guide improvements:
Cybersecurity SEO demands both visibility and trust. A secure and technically sound site supports that trust. Transparent processes like this show professionalism clearly. Competitors often rank because their technical setup is strong. A visible technical checklist signals depth and accountability.

Backlinks remain a strong ranking signal in competitive niches. Security companies often compete against high-authority domains. Many top competitors hold domain authority between seventy-five and eighty-five. Ranking beside them requires steady authority building.
Start with industry publications that serve security professionals. Contribute valuable insights to well-known cybersecurity blogs. Focus on quality over volume every time.
Consider these backlink strategies:
Avoid spammy link-building shortcuts completely. Automated link schemes damage credibility quickly. Manual outreach builds stronger and safer relationships. Personalize outreach messages with relevant value.
Original research performs especially well in this space. Security audiences appreciate real insights supported by data. Data-backed content attracts natural citations and shares. Authority grows when respected sites link to your work.
Competitor pages often emphasize structured link-building methods clearly. Authority remains a core ranking driver in this niche. Strategic backlinks strengthen visibility and long-term stability.
Not all security buyers search the same way. A CISO evaluates risk and compliance carefully. A founder often focuses on cost and scalability. An IT manager may search for technical deployment details.
Risk-driven searches are common in this industry. Buyers often search after hearing about new threats. They look for solutions that reduce exposure quickly. Your content should address urgent security concerns clearly.
Budget cycle searches also influence behavior. Many companies plan security spending annually. Content should reflect planning timelines and investment priorities. Address long-term value alongside immediate benefits.
Compliance deadlines create another search pattern. Buyers search before audits or regulatory reviews. They look for structured guidance and implementation clarity. Content should explain compliance alignment clearly.
Pain-point-driven searches reveal direct frustrations. Examples include phishing prevention failures or slow incident response. Address these problems with practical guidance and reassurance.
Competitors often segment startups and established brands carefully. Aligning with buyer intent improves relevance and engagement. Intent alignment increases conversions while supporting ranking performance.

Clear execution builds confidence and reduces uncertainty. Security companies want structured and predictable processes. They expect clear milestones and measurable outcomes. Transparency removes confusion and builds long-term partnerships.
When evaluating a cybersecurity SEO agency, buyers look for process clarity. They want to understand what happens each month. They also want proof of steady progress. A defined framework sets expectations clearly.
Use this five-step structure to guide execution:
Clients should always know what to expect. Reporting should remain easy to understand. Share clear KPIs such as keyword growth, organic traffic, and conversions. Avoid hiding behind complex dashboards or vague metrics.
Competitor pages often rank because they explain their process clearly. A transparent structure signals professionalism and reliability. In cybersecurity, trust builds before contracts are signed.
Growth without measurement leads to wasted effort. Security markets demand accountability and proof. Measurement turns strategy into predictable progress. It also helps identify what truly drives qualified leads.
Cybersecurity SEO must connect rankings with revenue outcomes. Traffic alone does not reflect business impact. Focus on metrics that reflect pipeline strength and sales influence.
Track these core performance indicators consistently:
Review metrics monthly and quarterly for trends. Look beyond traffic spikes and focus on sustainable growth. Identify content that drives strong conversions. Expand those themes into new clusters carefully.
Revenue attribution adds another layer of clarity. Connect SEO performance to sales results when possible. This builds internal confidence and budget support.
Scaling should follow proven success areas. Expand into new industries or verticals strategically. Replicate successful frameworks across similar services. Strong measurement supports confident scaling decisions.
Competitor pages often mention projections and timelines clearly. Measurement shows discipline and long-term commitment. Structured tracking signals maturity and strategic depth.
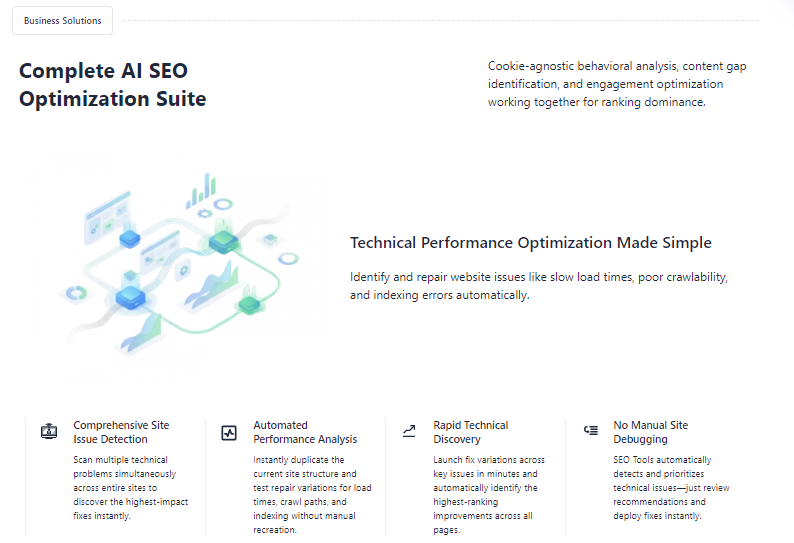
CasualFunnel helps connect SEO efforts to real business results. It tracks how organic visitors move toward demos and consultations. This shows which keywords and pages drive qualified leads, not just traffic.
By focusing on intent and conversions, it supports revenue-aligned SEO decisions. This clarity helps teams refine strategy and scale proven growth areas with confidence.
Growing in the security space requires more than basic SEO knowledge. The competition is strong and buyers expect precision. A structured system helps remove guesswork and improve results steadily.
CausalFunnel supports cybersecurity SEO with an intent-driven and data-backed approach.
You grow by targeting high-intent, long-tail keywords that real buyers actively search for, such as SOC 2 compliance support or advanced threat detection solutions. This ensures your content focuses on services people truly need, not broad traffic terms. You also benefit from cookie-agnostic AI that understands visitor behavior without relying on third-party data. This helps you tailor content for CISOs and IT managers based on real engagement patterns.
You strengthen E-E-A-T signals by improving content structure and clarity. This highlights your expertise and credibility, which are critical in security industries. You also identify technical SEO issues like crawl errors, slow load times, and indexing gaps. These fixes protect both performance and trust. AI-powered schema generation further improves visibility by helping your pages qualify for rich results.
By aligning search intent with behavioral insights, you attract qualified leads instead of casual visitors. You see stronger organic clicks, clearer performance signals, and reduced dependence on external data sources. This approach connects technical SEO, content relevance, and user behavior into one growth-focused system.
Many security companies struggle because they repeat common errors. Avoiding these mistakes saves time and budget. It also protects long-term credibility.
Avoiding these mistakes strengthens long-term positioning. Prevention often costs less than correction later.
Cybersecurity SEO requires patience, structure, and strategic discipline. The eight tactics in this guide work together. Keyword architecture builds topical clarity. Bottom-of-funnel pages drive qualified conversions. Technical optimization strengthens trust and usability. Authority building improves competitive positioning. Buyer intent alignment increases engagement and relevance. Transparent execution builds client confidence. Measurement connects effort with revenue impact.
Sustainable growth comes from consistent refinement and execution. Focus on steady improvements instead of quick shortcuts. Build authority through valuable insights and real expertise. Track results carefully and adjust based on data. With structured planning and long-term focus, your cybersecurity brand can compete confidently and grow predictably.
Cybersecurity SEO helps security companies rank for high-intent search terms. It focuses on trust, compliance, and technical buyers.
Cybersecurity buyers research longer and demand proof. Content must support risk, compliance, and complex decision processes.
Results take time due to long sales cycles. Most companies see steady gains within three to six months.
High-intent, long-tail keywords perform best. These include compliance, monitoring, and security service searches.
Success goes beyond traffic numbers. Track qualified leads, demos, and revenue influenced by organic search.
Start using our A/B test platform now and unlock the hidden potential of your website traffic. Your success begins with giving users the personalized experiences they want.
Start Your Free Trial
Empowering businesses to optimize their conversion funnels with AI-driven insights and automation. Turn traffic into sales with our advanced attribution platform.



